Network between instances
Principle of operation
The following steps assume that an instance of MITIGATOR has already been installed. Otherwise, perform installation using one of the following methods.
Interaction between instances is arranged through Wireguard. A virtual network (VPN) is created between instances.
Each instance has a key pair: a private key and a public key.
The private key is stored only on its instance in vpn-private.conf.
The public keys of all instances are listed in vpn-public.conf,
which must be the same on all instances.
It also contains the addresses of the instances and their addresses in the VPN.
The VPN instance address is also specified as MITIGATOR_VPN_ADDRESS in .env.
The gateway component is responsible for organizing the VPN. When
clustering is not applied, it does not create a VPN. When clustered,
it configures the VPN according to vpn-private.conf, vpn-public.conf, MITIGATOR_VPN_ADDRESS.
If you need to change gateway settings other than *.conf, you need to
completely restart the instance (docker-compose down && docker-compose up -d).
See below for a specific command
to update the VPN configuration.
System preparation
Kernel module
Ubuntu 20.04 LTS includes Wireguard in the base distribution. No additional steps are needed.
Debian 10 (Buster) requires a ported package to be installed:
echo deb http://deb.debian.org/debian buster-backports main > /etc/apt/sources.list.d/buster-backports.list
apt-get update
apt-get install linux-headers-amd64 wireguard-dkms
You can check support with the modprobe wireguard command. If nothing is printed
in response, the module is available. In this case, it is enough to configure its
automatic loading. Otherwise, a reboot is required.
To add wireguard to automatic download:
echo wireguard >> /etc/modules-load.d/mitigator.conf
Instruments
Install wg utility:
apt-get install wireguard-tools
Instance setup
All of the files are created in /srv/mitigator catalog.
If more than the first instance is configured, the vpn-public.conf file
must be taken from any of the configured instances to complete it.
-
Create the private key (Resulting example:
yDPg5doavYH7fdD86nt+cOzSBL4znVZcrcrJwjY/Xmw=):wg genkey -
Write the key in
vpn-private.conf:[Interface] ListenPort = 4567 PrivateKey = yDPg5doavYH7fdD86nt+cOzSBL4znVZcrcrJwjY/Xmw=The specified port 4567 must be open for UDP traffic.
-
Get public key from private key (Resulting example:
acfzxE6ZsiYE4jIqsBicOt7oT8ZuKhxBvuz0+6JxiEc=):echo 'yDPg5doavYH7fdD86nt+cOzSBL4znVZcrcrJwjY/Xmw=' | wg pubkey -
Add a section with the public key and instance addresses to
vpn-public.conf(create a file if this is the first instance):[Peer] PublicKey = acfzxE6ZsiYE4jIqsBicOt7oT8ZuKhxBvuz0+6JxiEc= AllowedIPs = 10.8.3.1/32 Endpoint = 192.0.2.1:456710.8.3.1is an instance address inside VPN. Must be unique among all instances. All addresses must be within the same /24 network (default).192.0.2.1:4567is the external address of the instance and the port configured above. Other instances will send UDP packets to this address and port. -
Create a
docker-compose.vpn.ymlfile with the exactly following content:version: "2.2" services: gateway: environment: GATEWAY_ADDRESS: "${MITIGATOR_VPN_ADDRESS:-10.8.3.1}/${MITIGATOR_VPN_PREFIX:-24}" volumes: - ./vpn-public.conf:/srv/public.conf:ro - ./vpn-private.conf:/srv/private.conf:ro -
Add this file to the list of Docker Compose configurations in
.env:COMPOSE_FILE=docker-compose.yml:docker-compose.vpn.ymlIf more files are used, such as
docker-compose.override.yml, they must all be listed separated by colons. -
Add the address of the instance inside the VPN to
.env:MITIGATOR_VPN_ADDRESS=10.8.3.1It must match the one configured in
vpn-public.conf. Also, this address must be specified in the instance settings in the MITIGATOR web interface.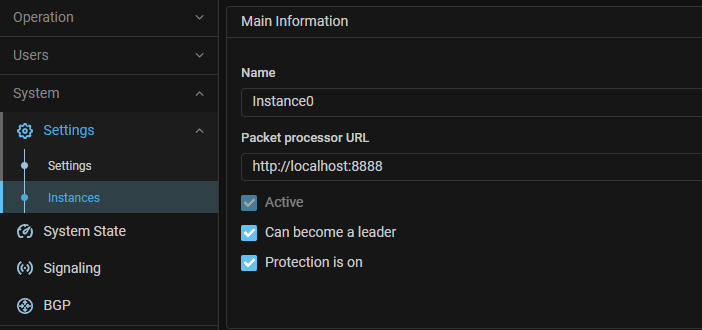
-
Reboot MITIGATOR:
docker-compose down && docker-compose up -d
Cluster setup after adding an instance
After adding a new instance to the vpn-public.conf file,
you need to make changes on all instances.
On each instance, you need to update the VPN configuration without restarting:
docker-compose exec gateway reconfigure