Version v26.04
Update to version v26.04 must be performed according to special instructions.
Version v26.04 adds: automatic packet capture in General Protection, ISN-agent improvements, dynamic sFlow sampling, Flow/SNMP ratio page in Collector, GRE traffic processing distribution mode across cores, traffic bypass mode above the license bandwidth, traffic graphs from internal network in protection policies, updated PostgreSQL version.
The functionality of ACL, ACL6, ACLI, LACL, LACL6, SCAN, ATLS, ITLS, SPLI, DNS, DNS6, TCP6, USF, BPF, LIM countermeasures has been expanded, as well as Collector, HPD, PCAP, “Overview” page, “Flow Analysis” page, “Event Log”, and named filter rule sets.
Multiple UX improvements made.
Changes in v26.04
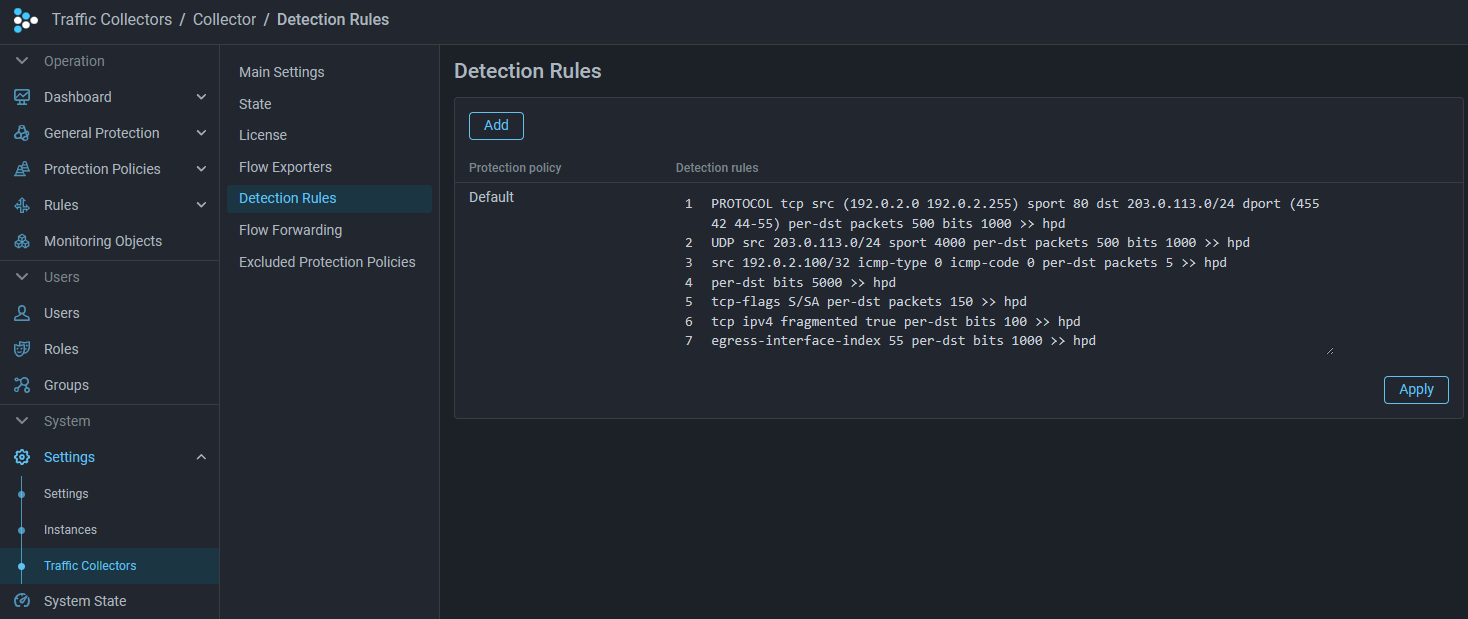
HPD. Host Protection Detector
Added ability to mark traffic in HPD based on Collector data
Added logging of HPD activation reason
Now the Host Activation Log stores not only the fact of activation of the mechanism for a specific IP address, but also the reason for activation and the rule, if present.
instance_id,instance_name,created_at,action,dst_ip,reason,rule
1,Mitigator0,2022-09-02 10:44:31.53622 +0000 UTC,added,10.0.2.254,LimitBps,BITS 200 ACL udp
1,Mitigator0,2022-09-02 10:44:41.51245 +0000 UTC,added,10.0.2.254,UntrustedSource,Increased maximum bit limit
Autodetection
Added test mode disabling by the autodetection mechanism
Added <element>.TestMode.* thresholds that control the countermeasure’s test mode operation.
The logic of their operation is identical to that of thresholds without TestMode in the name,
except for naming nuances:
- For bidirectional thresholds, the relationship
Xxx.TestMode.Yyy.On < Xxx.TestMode.Yyy.Offtypically holds, because it makes sense to turn off test mode when the threshold is exceeded, and turn it on when traffic drops below a certain mark. - In
Diffthreshold sets for absolute change per cycle,OnFactorandOnMin*are present instead ofOffFactorandOffMin*, having the same meaning but applicable to enabling test mode. - In
Ratiothreshold sets for relative change per cycle,Xxx.TestMode.Yyy.Ratio.On < Xxx.TestMode.Yyy.Ratio.Off, because it makes sense to turn off test mode when traffic grows sharply.
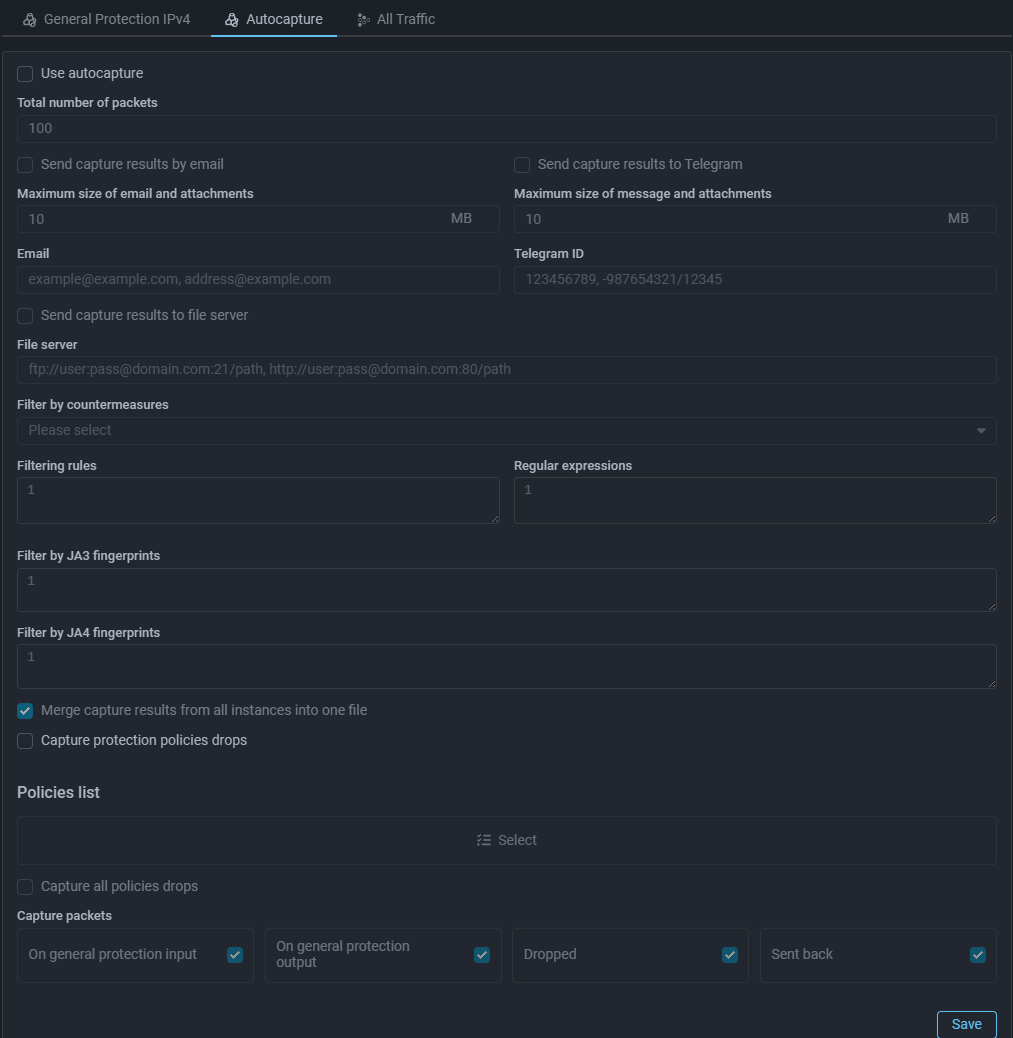
PCAP
Added automatic packet capture in General Protection
Changed automatic PCAP deletion time
Protection Policies
Added traffic graphs from internal network in protection policies
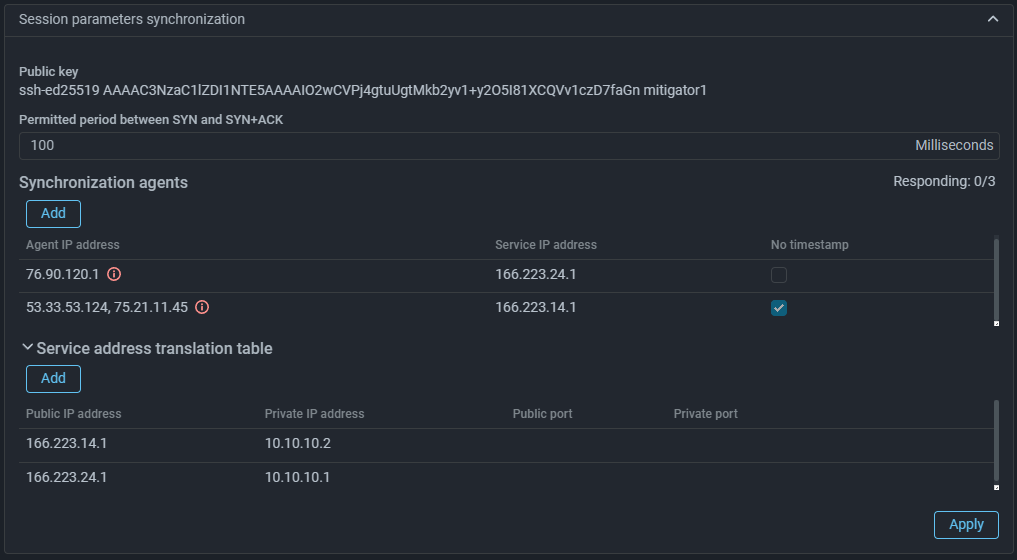
Added TCP Timestamps option check by ISN-agent
Now when checking SYN+ACK packets, you can select processing mode without taking Timestamp into account.
Since not all servers send Timestamp, the check can be disabled by setting the flag “No timestamp” in the session parameter synchronization settings for a specific server. The parameter applies to all servers listed in the line. If you need to apply it to only one server, you need to move it to a separate entry. If the synchronization agent is used in multiple protection policies, and in at least one of them the “No timestamp” parameter is set, it will be applied in all policies.
Countermeasures
BPF. Removed VLAN ID functions in mitigator_bpf.h
VLAN ID functions have been removed from the public API of BPF programs. If these functions were used in your BPF programs, when rebuilding them with the new mitigator_bpf.h header, you need to add these functions to the program source code:
#define VLAN_ID_MASK 0x0fff
/** @brief Get VLAN ID from 802.1q header. */
LOCAL uint16_t
vlan_get_id(const struct VlanHeader* vlan) {
return bswap16(vlan->control) & VLAN_ID_MASK;
}
/**
* @brief Set VLAN ID in 802.1q header.
*
* If you don't need to keep rarely used DEI and PRI, a faster alternative is:
* @code
* vlan->control = bswap16(id);
* @endcode
*/
LOCAL void
vlan_set_id(struct VlanHeader* vlan, uint16_t id) {
uint16_t bits = vlan->control & ~bswap16(VLAN_ID_MASK);
vlan->control = bswap16(bswap16(bits) | id);
}DNS. Added graphs by request types
USF. Changed tracked sessions graphs
Now the countermeasure graphs display the number of sessions observed both inside and outside the recent session ignore depth window:
-
USF Allowed sessions— number of tracked sessions that were observed outside the recent session ignore depth window; -
USF Ignored sessions— number of tracked sessions that were observed only inside the recent session ignore depth window.
SCAN. Added the ability to set the number of unique destination IP addresses and ports
ACL. Added icmp6 alias support in rules
icmp6 instead of protocol 58.
ACL. Added BYPASS and COUNT BYPASS actions
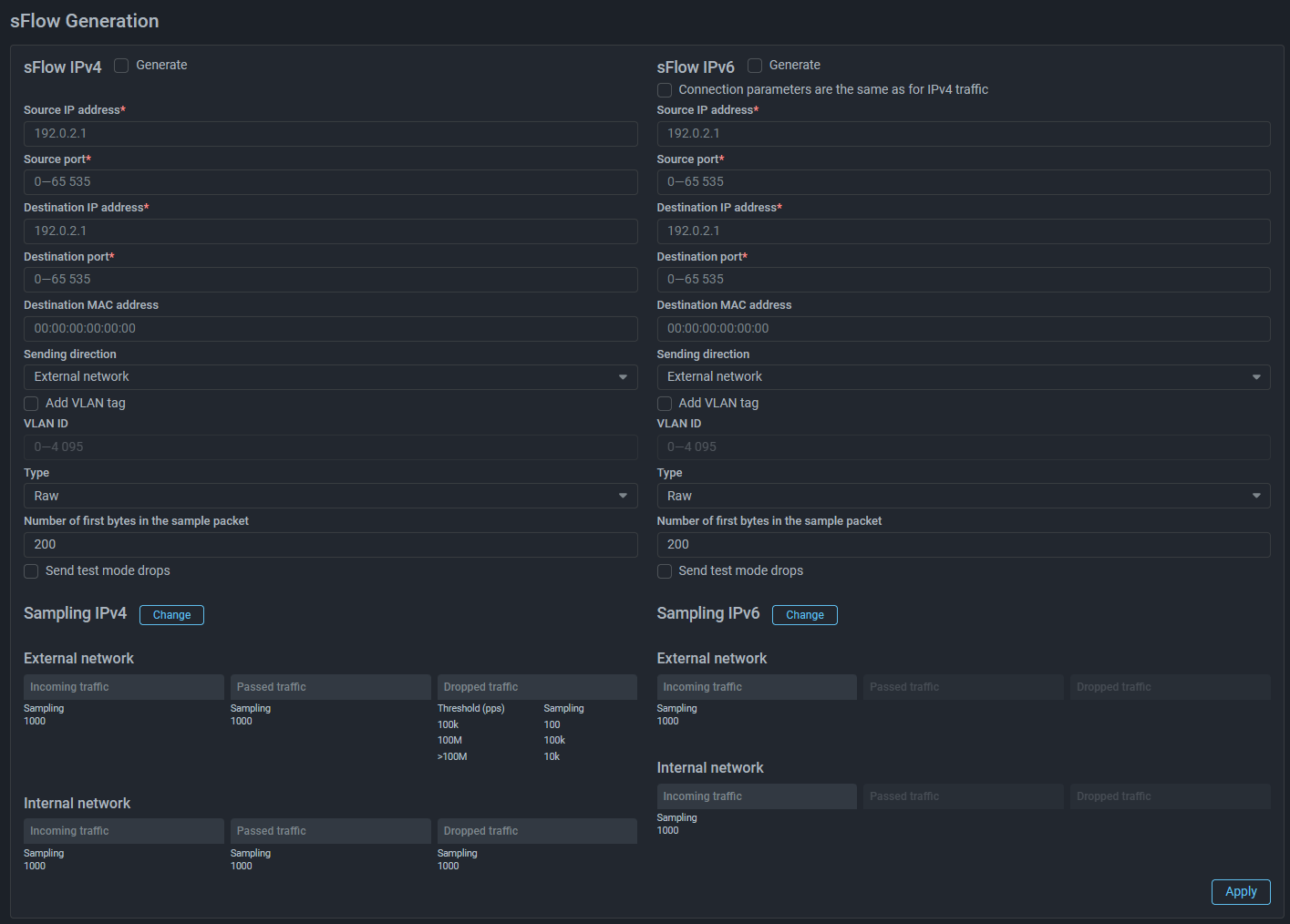
sFlow
Collector
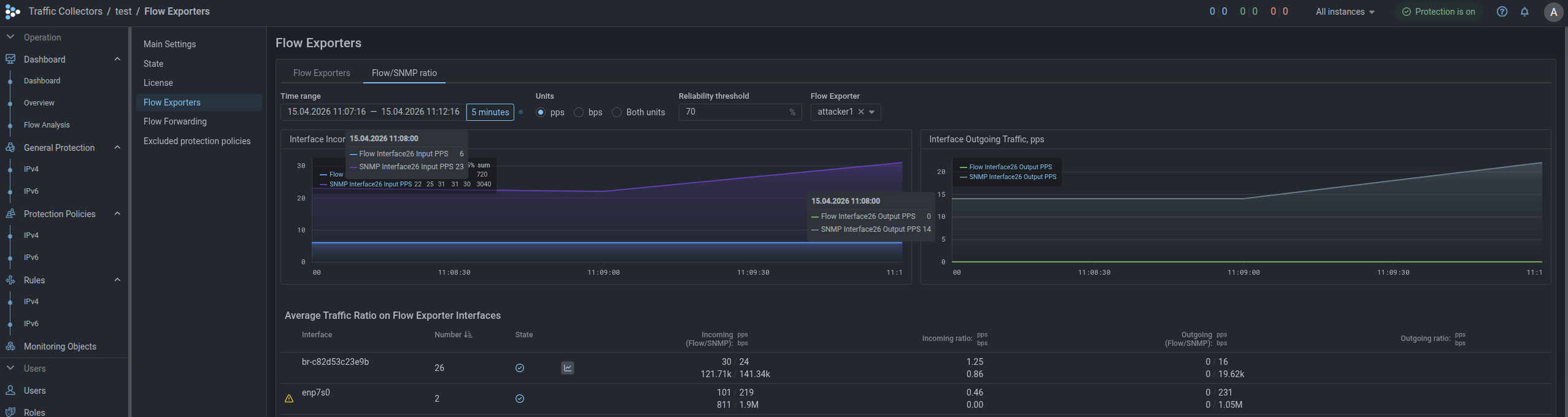
Added page for displaying average traffic ratio on Flow source interfaces
A “Flow/SNMP Ratio” tab has been added to the “Flow Exporters” page, displaying traffic statistics on all source interfaces obtained via Flow and SNMP.
The tab also specifies the “Allowable deviation”, which determines how much the ratio of the average traffic rate obtained via Flow to that obtained via SNMP can deviate from one. For example, with a tolerance of 10%, a ratio between 0.9 and 1.1 is considered normal.
If the deviation in the ratio of average traffic rate values received via Flow to those received via SNMP exceeds the acceptable limit, this may indicate that the system is configured incorrectly or that data is not being received. For such interfaces, appropriate indication appears in the row.
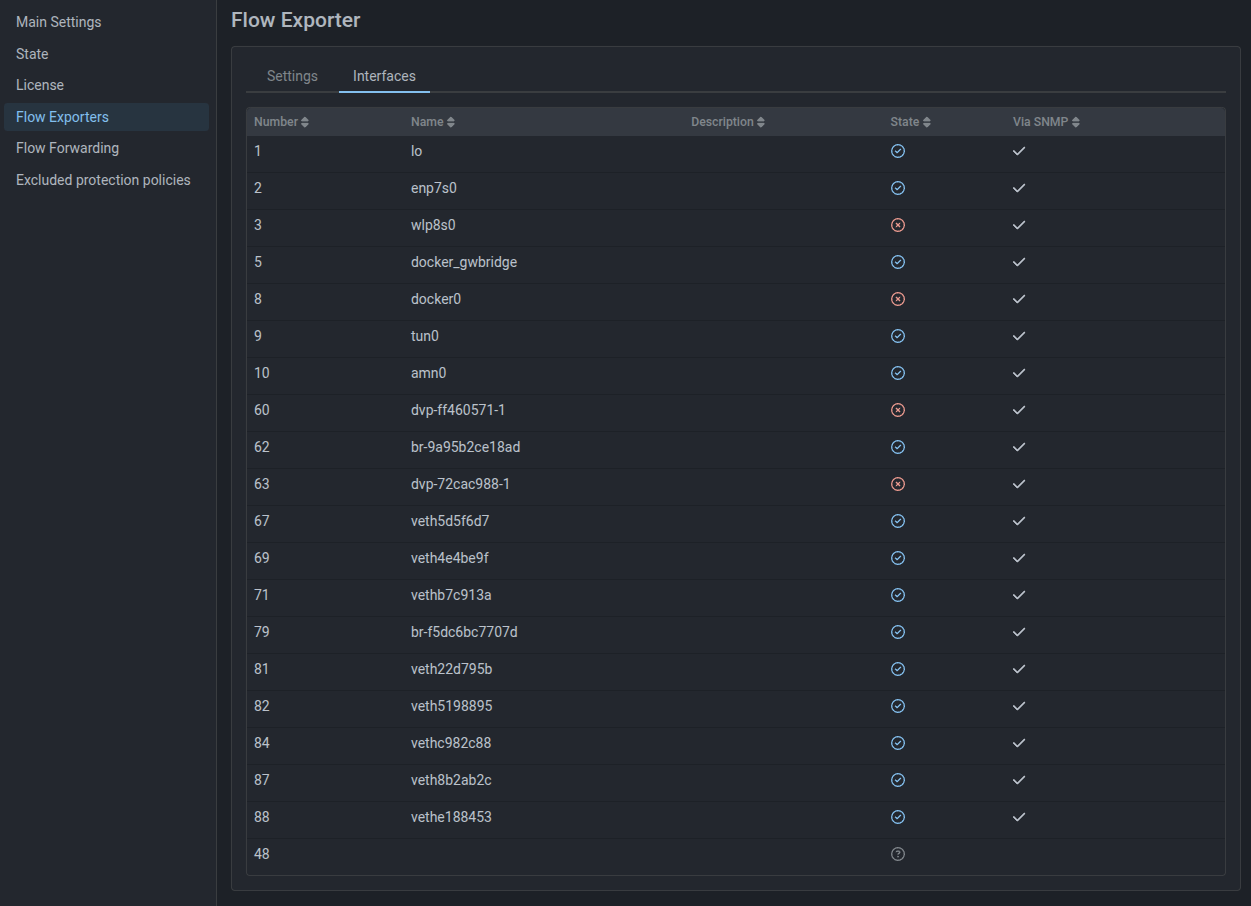
Added new Flow source interface status
Now in the “Status” column of the Flow source interfaces table, the interface displays one of three statuses based on SNMP data:
- interface status UP;
- interface status DOWN;
- interface status unknown.
Logan
Added negation in regular expressions
Now in rules for request, referer and user-agent components you can specify negation using the “not” keyword.
Examples:
# Block IP address for 300 seconds that requested any URI from web-server except
# `/api/some/magic/uri`:
block 300 not request /api/some/magic/uri
# Block IP address for 600 seconds that received
# request containing any value other than 123 in User-Agent header:
block 600 not user-agent 123
# Create entry in event log when receiving from IP address
# request containing any value other than "^https://domain" in Referer header:
alert not referer "^https://domain"Core
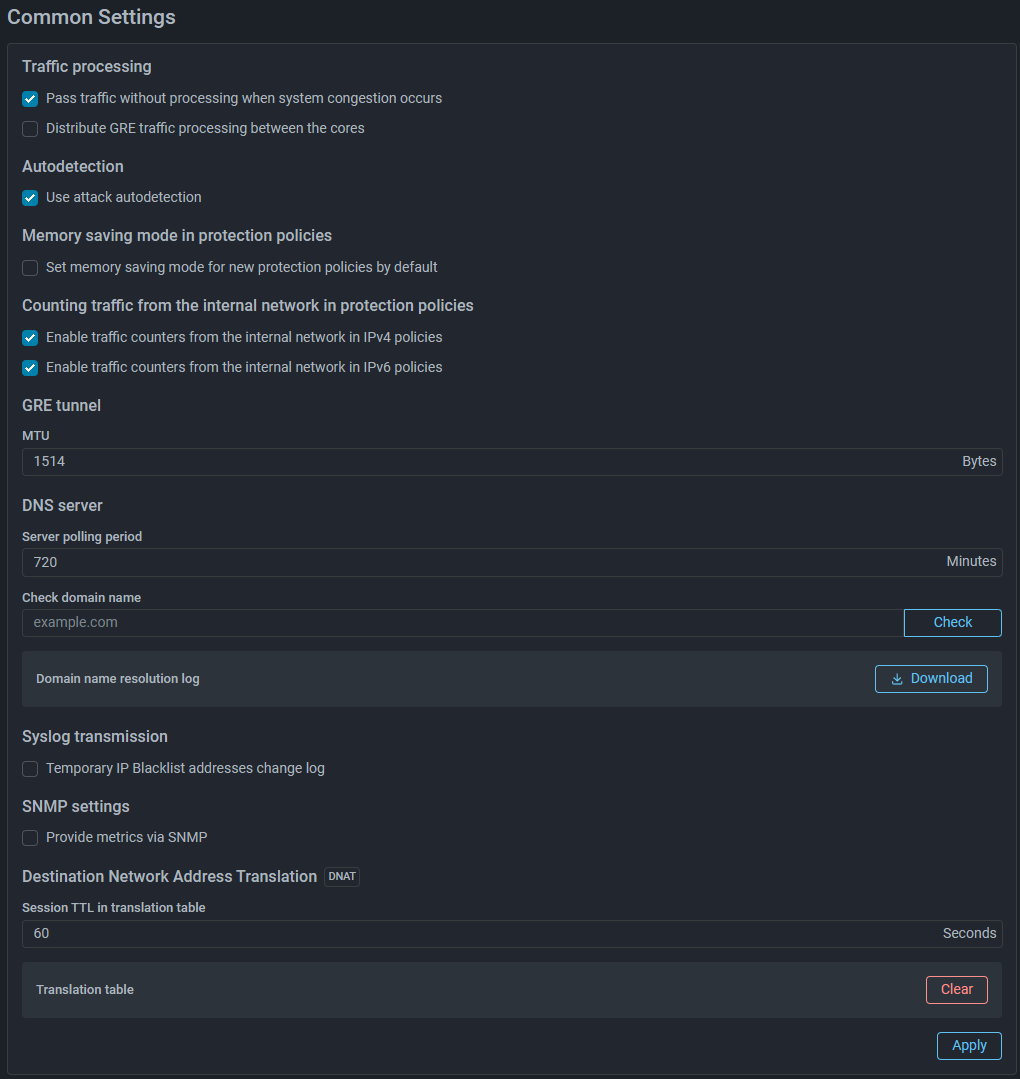
Added mode for distributing GRE traffic processing across cores
When activating the “GRE Tunnel with External Service” function in instance settings, GRE traffic processing is by default performed on a single CPU core. If the flag is set, balancing across all cores will be performed. The setting is applicable only when using Mellanox network cards, for other network cards the setting is ignored.
Updated PostgreSQL version
Changed pgfailover configuration logic
Previously, pgfailover parameters were set in the command: of the pgfailover
service in docker-compose.failover.yml. When updating the file, user changes
had to be migrated manually.
Now pgfailover parameters are set via environment variables in .env, and a
non-standard server list — in docker-compose.override.yml.
For future updates, simply download the latest docker-compose.failover.yml.
ISN-agent
Updated ISN-agent for version v25.06+
Data Synchronization
Added DNAT support via active synchronization mechanism
Added DNAT support via table synchronization mechanism
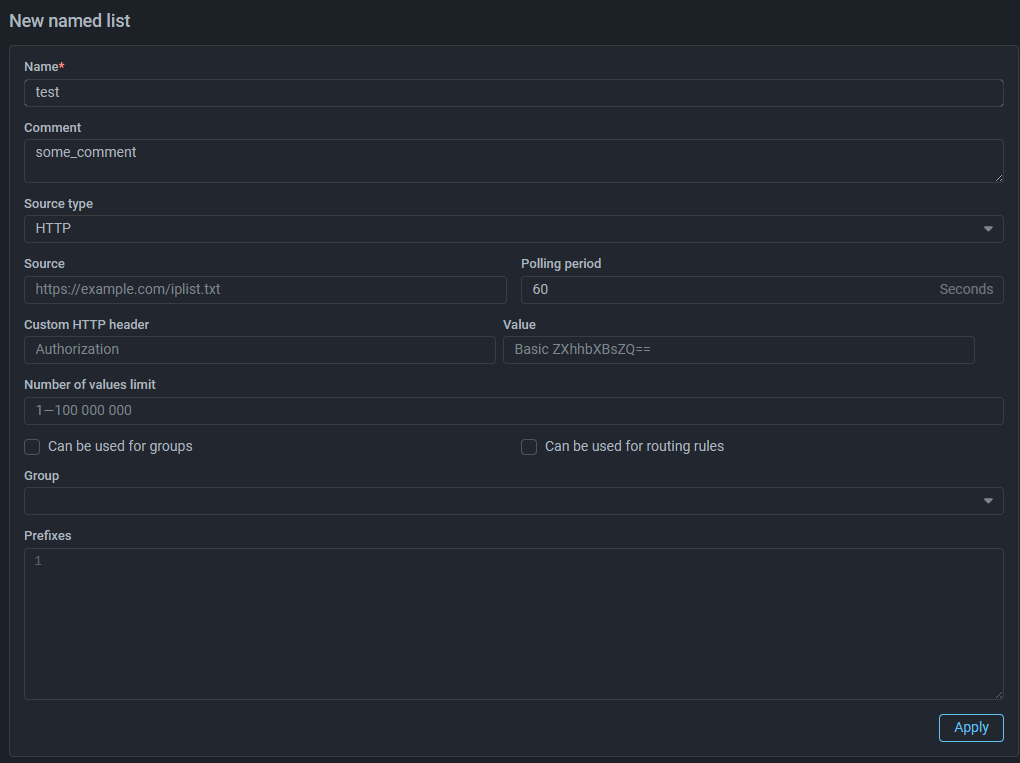
Named Lists
Added size limit for rules in named ACL Rule Sets
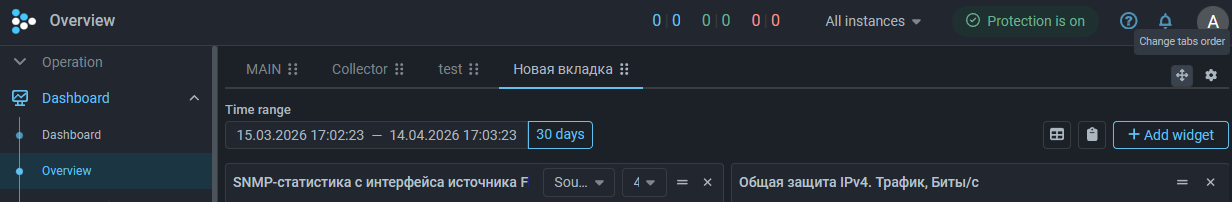
"Overview" Page
"Flow Analysis" Page
Added widget category for building graphs on passed traffic
Event Log
Added logging of packet capture file paths
Added token logging when ALERT action triggers in Logan
Interface
Added ability to set threshold values with different decimal prefixes
To improve convenience of setting thresholds and simplify perception of already set ones, the ability to change decimal prefixes when specifying values has been added.
As an experiment, currently the functionality has been added to HPD, BPF, LIM and TAP interface, we plan to extend this change to all other mechanisms and countermeasures in the future.
Unified date and time order in fields displaying action execution time
Now in all interface elements where date and time of action execution were specified,
the order is identical: yyyy-mm-dd HH:MM:SS.